
门罗的安全
成立一年
2013阶段
E系列 |活着总了
250.5美元估值
0000美元最后提出了
100美元 | 2年前门罗的安全产品视频


与门罗的安全?
确保您的公司和产品在我们的平台上得到准确的展示。
门罗的安全的产品和差异化
安全网络网关
Menlo SWG采用了零信任原则,将威胁从用户那里隔离开来,并始终保持在下一次攻击之前,消除了允许或阻止创可贴的需要。
研究包含门洛安全
从CB Insights情报部门获得数据驱动的专家分析。德赢体育vwin官方网站
德赢体育vwin官方网站CB Insights情报分析师曾提到Menlo Security1 德赢体育vwin官方网站CB Insights研究简报,最近在2022年3月10日.
2022年3月10日
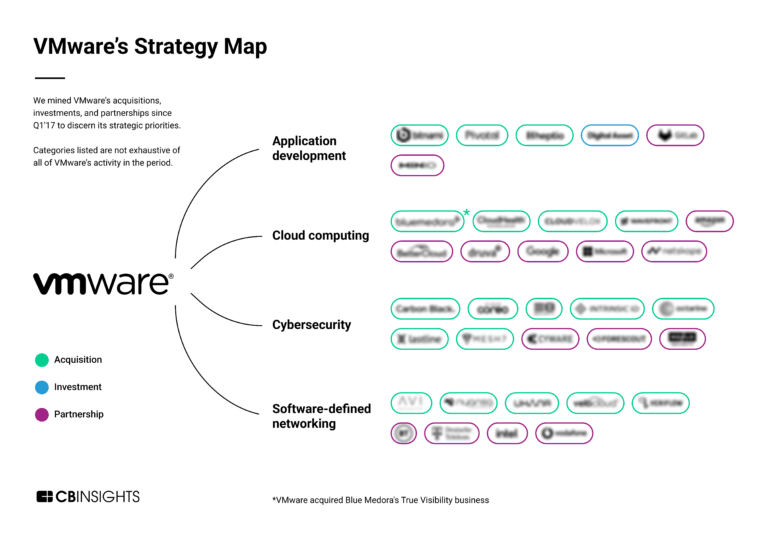
分析VMware的增长战略:这家科技公司如何适应云计算的未来专家集合包含门洛安全
专家收藏是由分析师策划的列表,突出了你在最重要的技术领域需要了解的公司。
Menlo Security包括在内2专家收藏,包括科技公司IPO计划.
科技公司IPO计划
282件
跟踪和获取公司信息和工作流程。
网络安全
5260件
最新的门罗的安全新闻
2023年1月3日
Brett Raybould EMEA解决方案架构师,Menlo安全检测一直是网络安全战略的关键组成部分。通常,组织采用分层方法进行检测,使用各种解决方案,包括防病毒软件、沙盒引擎、大数据分析、异常检测等。这些技术用于发现和发现任何恶意软件或恶意代码,可以到达端点并消除它。在检测解决方案的情况下,眼见为实。如果你不能检测到威胁,你怎么知道它是否真的是威胁?这是此类技术构建、搜索和仅对网络上检测到的威胁采取行动的核心原则,并在确认威胁后将其隔离和消除。不幸的是,这种方法产生了几个问题。检测解决方案侧重于确定哪些是恶意的,哪些是良性的,这导致它们受到类似的限制。事实上,它们很容易产生假阳性和假阴性,而且将这些技术叠加在一起的成本很高。不仅如此,仅仅依靠检测还会使您处于不利地位,迫使您在威胁行为者已经进入网络时做出反应——到那时,往往为时已晚,损害已经造成。 Attackers Are Overcoming Legacy Security Solutions With the continued belief that an array of detection solutions is adequate, many firms have failed to add capabilities to their network security technology stack, relying on the same solutions and strategies that are simply no longer fit for purpose. While many organizations have stood still, threat actors have continued to tweak and adapt their methods, now leveraging attack techniques capable of bypassing legacy network security defenses. The use of Highly Evasive Adaptive Threats (HEAT) is becoming increasingly common, for example, with criminals leveraging one of four evasive techniques to deliver malicious payloads to endpoints: HTML smuggling and/or JavaScript trickery within browser environments. Sending malicious links to users through communication mediums outside of email, such as social media SMS and shared documents. Tampering with benign websites to create ‘Good2Bad’ websites for brief periods to dodge web categorization. Using malicious content, such as images impersonating known brand logos that can be generated using JavaScript in the browser by its rendering engine to avoid detection from static signatures that examine web page source code and HTTP traffic. Indeed, the success of these methods has been proven in several notorious attacks that have taken place in recent years. The Astaroth banking Trojan that has been an issue since 2017 uses HTML smuggling to sneak malicious payloads past network-based detection solutions, for example. Meanwhile, the Gootloader campaign that the Menlo Labs team tracked in the early phase of 2022 leveraged SEO poisoning to generate high-level page rankings for compromised websites. Embracing a Multi-Faceted Approach to Security From file inspections performed by SWGs and sandboxes to network and HTTP-level inspections, indicator of compromise (IOC) feeds and malicious link analysis, many typical defense mechanisms that form central pillars of many organizations’ security strategies are rendered almost useless when confronted with HEAT. To be properly protected against modern threats, organizations must shift to a multi-faceted approach to security that moves beyond a sole reliance upon detection solutions. While these solutions still serve a purpose, they must be combined with an emphasis on prevention to ensure that attackers are blocked from reaching networks in the first instance. Unlike detection solutions, prevention solutions do not work to determine whether traffic is good or bad. Instead, they take a zero trust approach in assuming that all traffic has at least some risk attached to it and therefore treat all traffic as guilty until proven innocent. This is the case with remote browser isolation (RBI) – an innovative method focused on preventing code from reaching the users without determining whether that code is infected or not. With RBI, the point of execution for active content is moved to a disposable, cloud-based container, preventing any malicious content from successfully reaching its target, creating something of a digital air gap that allows users to browse the internet safely. When all traffic is executed in the cloud, it doesn’t come anywhere near the endpoint, drastically reducing the issues in dealing with costly and time-consuming alerts hitting your SOC which need to constantly be analyzed and remediated. Simply put, it doesn’t matter if there is a vulnerability on the endpoint for attackers to exploit or bypass with HEAT techniques. By ensuring no content can reach the network, no payloads can execute. Related to This Story
门罗的安全常见问题
Menlo Security是什么时候成立的?
Menlo Security成立于2013年。
门洛保安公司的总部在哪里?
Menlo Security总部位于山景城El Camino Real 800 W。
Menlo Security的最新一轮融资是多少?
Menlo Security的最新一轮融资是E轮。
Menlo Security筹集了多少资金?
Menlo Security共融资2.505亿美元。
门洛保安公司的投资人是谁?
Menlo Security的投资者包括General Catalyst、Vista Equity Partners、Neuberger & Co. Ventures、摩根大通证券(J.P. Morgan Securities)、Osage University Partners等8家公司。
Menlo Security的竞争对手是谁?
Menlo Security的竞争对手包括Netskope、AppOmni、Cyolo、Illumio、Salt Security、BetterCloud、Perimeter 81、VMware、Traceable AI、WatchGuard Technologies等54家公司。
Menlo Security提供什么产品?
Menlo Security的产品包括安全网络网关和其他4种。
比较门洛安全与竞争对手

Netskope提供基于云的安全平台。它在访问云服务、网站和私有应用程序时提供可见性、数据和威胁保护。该公司提供转型解决方案、安全现代化解决方案、框架解决方案和行业解决方案。它还提供广泛的产品,如无界广域网、物联网安全、SaaS安全态势管理、数字体验管理等。该公司成立于2012年,总部位于加利福尼亚州的圣克拉拉。

Perimeter 81提供安全服务边缘(SSE)和零信任网络访问(ZTNA)解决方案。其平台提供即时部署、统一管理和360度可视性服务。它为包括医疗保健和金融在内的广泛行业的客户提供服务。它成立于2018年,总部位于以色列特拉维夫。

Iboss提供解决方案,保护数以千计的企业、服务提供商和政府网络免受新时代的网络威胁。该公司的安全Web网关平台具有先进的架构,由超过75项专利和正在申请的专利支持,被全球超过4000家企业选择,以提高他们的安全状况。
在整个威胁生命周期中,Forcepoint保护用户、数据和网络免受最坚定的对手的攻击,从意外或恶意的内部威胁到外部攻击者。Forcepoint保护数据无处不在-在云端,在路上,在办公室-简化合规,使更好的决策和更有效的补救。

AppOmni是企业级SaaS安全的提供商。该公司使用api、安全控制和配置设置来评估SaaS部署的当前状态,使组织能够为数据访问、数据共享和持续自动验证的第三方应用程序建立规则。它为技术、医疗保健、银行和安全部门的企业提供服务。AppOmni成立于2018年,总部位于加利福尼亚州旧金山。

Lacework是一家后期技术公司,为整个IT基础设施开发了完整的安全平台,从DevOps和编排环境到云和混合工作负载。Lacework旨在自适应云不断变化的配置,以提供可见性和入侵检测,帮助企业保持其数据和资源的安全。该公司服务于各种需要入侵检测的行业。Lacework成立于2015年,总部位于加利福尼亚州圣何塞。
为您的团队发现正确的解决方案
CB I德赢体育vwin官方网站nsights技术市场情报平台分析供应商、产品、合作伙伴和专利的数百万个数据点,帮助您的团队找到他们的下一个技术解决方案。
